FindSec Cybersecurity
Our Mission: Freedom — From The Limitations of Traditional Cybersecurity
What We Do
Your Security is Important to Us

Penetration Testing
Our team of penetration testers at FindSec can detect cybersecurity vulnerabilities proactively, preventing potential intrusions into your network or computer system.

Cybersecurity Consulting
Our Cybersecurity Consulting services at FindSec bring extensive experience from working on projects for some of the world's largest organizations, providing invaluable support to your business.

OS Forensics
OS forensics is the art of investigating digital devices to uncover evidence, track user activities, and analyze system data for legal or security purposes.

Data Recovery
Data recovery services help retrieve lost or corrupted data from storage devices, ensuring critical information is restored promptly and efficiently.

Virtualization Security
Protecting virtualized environments, ensuring the isolation, integrity, and confidentiality of virtual machines and their data.

Sandbox
A security sandbox is a controlled environment for safely executing untrusted software, providing analysis and protection against potential threats in a virtual container.

IoT Device Penetration Testing
IoT Device Penetration Testing: Assessing the security vulnerabilities of Internet of Things (IoT) devices to ensure protection against potential cyber threats.

EDR and XDR
Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) are cybersecurity services. EDR focuses on monitoring and securing individual devices, while XDR extends this to broader network and cloud environments.
Mobile Application Security
A range of solutions designed to safeguard your mobile apps from cyber threats. These services include vulnerability assessments, code reviews, penetration testing, and security consultations.
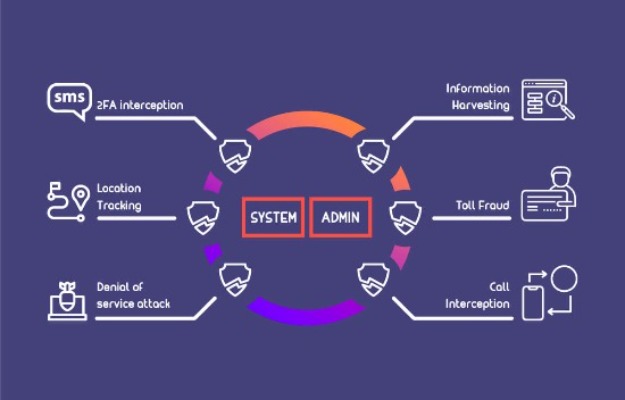
Network Security
Network security services protect the communication pathways between devices and systems, using technologies like firewalls, intrusion detection systems, and VPNs.






